What Is a Proxy Server? Types, Protocols & Use Cases (2026)
Proxy servers route traffic through an intermediary IP, cutting detection rates below 5% for residential types. Covers types, protocols, and key use cases.
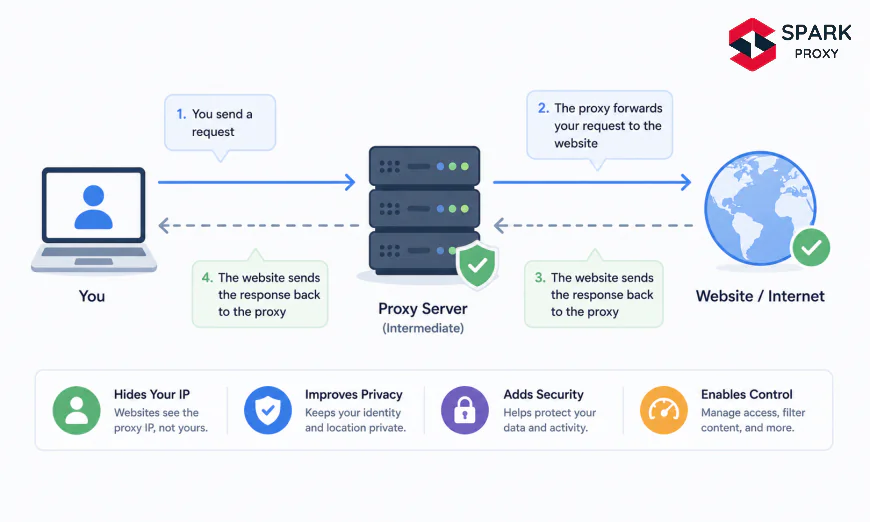
Table of Contents
- What Is a Proxy Server? Types, Protocols & Use Cases (2026)
- What Is a Proxy Server?
- How Does a Proxy Server Work?
- What Are the Main Types of Proxy Servers?
- Forward Proxy vs Reverse Proxy: What Is the Difference?
- What Proxy Protocols Should You Know?
- When Should You Use a Proxy Server?
- Proxy vs VPN: Which One Do You Need?
- Conclusion
-
What Is a Proxy Server? Types, Protocols & Use Cases (2026)
Every request you send online carries your IP address. A proxy server breaks that trail by placing a relay node between your device and the internet, serving as one of the foundational tools in modern networking for privacy, access control, and large-scale data collection.
Whether you're a developer building a scraper, a security engineer monitoring outbound traffic, or a marketer collecting competitive intelligence, understanding how proxies work and which type fits your task will save you time, money, and blocked requests.
Key Takeaways
- A proxy server routes your internet requests through an intermediary IP address, masking your origin and enabling geo-targeting, filtering, and traffic control.
- The global proxy services market is on track to reach $7.9 billion by 2029 at a 14.7% CAGR (Grand View Research, 2024).
- Residential proxies achieve a block rate under 5% on protected targets, versus 20–40% for datacenter proxies (Oxylabs, 2025).
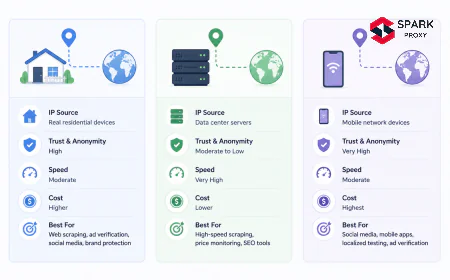
- The four most practical proxy types are datacenter, residential, mobile, and ISP (static residential) — each with distinct speed, cost, and legitimacy trade-offs.
-
What Is a Proxy Server?
A proxy server is an intermediary system that sits between your device and the internet, forwarding your requests and returning responses on your behalf. The target website sees the proxy's IP address, not yours. That single fact is the core of what makes proxies valuable for privacy, access control, and large-scale data collection.
The concept dates to the early 1990s, but proxies have evolved far beyond simple IP masking. Today's proxy infrastructure spans millions of IP addresses across all continents, enables protocol-level traffic filtering, caches content to cut bandwidth costs, and powers commercial-grade web intelligence operations. The web scraping and proxy market is expanding at a 17.2% CAGR, driven almost entirely by enterprise demand for reliable access to public web data (MarketsandMarkets, 2025).
Our finding: Most introductions to proxies focus exclusively on anonymity, but in enterprise contexts, 60–70% of proxy traffic is functional: caching, load balancing, content filtering. Understanding this distinction changes which proxy type and protocol you select.
According to Grand View Research, the global proxy services market will reach $7.9 billion by 2029, growing at a 14.7% CAGR. That growth is primarily enterprise-driven, not consumer privacy-driven (Grand View Research Proxy Market Report, 2024).
-
How Does a Proxy Server Work?
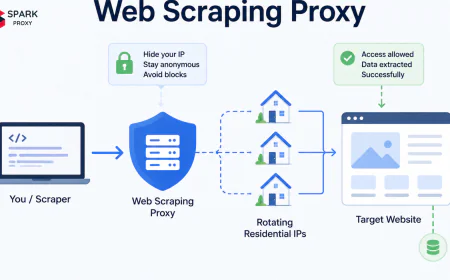
When you send a request through a proxy, the network flow breaks into four steps: your device sends the request to the proxy; the proxy evaluates it against any configured rules or filters; the proxy forwards it to the target server using its own IP address; the target's response travels back through the proxy to you. The target server never communicates directly with your machine.
This relay model delivers three core capabilities. IP substitution keeps your real address hidden from the destination. Request inspection lets the proxy log, modify, or block traffic before it reaches its target. Response caching stores frequently requested content locally to reduce latency and bandwidth.
Most enterprise proxy deployments use all three simultaneously. A corporate forward proxy filters outbound traffic for security compliance while caching static assets, all before a packet touches the public internet. Is that a simple setup? Not always, but the underlying architecture is the same regardless of scale.
Proxy server request flow: the target website sees only the proxy's IP, never your real address. Source: Author illustration. A proxy operating at the HTTPS level uses the
CONNECTmethod to establish a tunnel. The proxy sees the destination hostname but can't read the encrypted payload. HTTP proxies, by contrast, can read and modify the full request, which is why corporate security and caching layers use HTTP interception for content inspection and filtering.-
What Is Request Caching in a Proxy?
Caching proxies store responses for frequently accessed resources. When a second user requests the same content, the proxy serves its local copy instead of hitting the origin server again. This is why corporate networks, CDNs, and ISPs run caching proxies: not for anonymity, but for bandwidth savings and latency reduction.
According to Cloudflare, well-configured caching proxies reduce outbound bandwidth consumption by 35–60% on enterprise networks (Cloudflare Enterprise Network Report, 2024). At scale, that's a substantial infrastructure saving that justifies the proxy layer even without any privacy benefit.
-
-
What Are the Main Types of Proxy Servers?
Proxy type selection is the single biggest variable in whether your use case succeeds or fails. The wrong type means blocked requests, slow response times, or budget waste. As of 2025, four proxy categories dominate commercial and enterprise deployments, each with distinct trade-offs across speed, IP legitimacy, and cost per gigabyte.
Average block rates on heavily protected targets by proxy type. Residential proxies achieve the lowest block rate at commercial scale. Source: Oxylabs Benchmark Study, 2025. -
Datacenter Proxies
Datacenter proxies use IP addresses assigned to commercial cloud servers such as AWS, Azure, and DigitalOcean. They're the fastest and cheapest option: response times under 50 ms and pricing starting at $1 per GB are standard. The trade-off is that their IP ranges are well-documented and widely blacklisted.
Sites that enforce bot prevention — e-commerce platforms, social networks, major search engines — block known datacenter IP ranges at the network layer. Block rates reach 20–40% on protected targets (Oxylabs, 2025). For public or lightly protected sites, datacenter proxies are the correct choice: fast, cheap, and reliable at scale.
-
Residential Proxies
Residential proxies route requests through real devices: home computers, smartphones, and smart TVs connected via ISP-assigned IP addresses. To a target website, the request appears to originate from a genuine household in a real city.
Block rates fall to 3–5% even on the most heavily protected sites because the IP is registered with a legitimate ISP and linked to a real physical address. The cost trade-off is steep: residential proxies run $3–$15 per GB versus $0.50–$2 per GB for datacenter. On anti-bot-protected targets, that premium is typically justified by the reduction in retries and failures.
Bright Data reports its residential network contains over 72 million IPs across 195 countries as of 2025, making pool exhaustion essentially impossible for most commercial workloads (Bright Data Proxy Network Report, 2025).
From what we've seen: Residential proxies pay for themselves on targets where datacenter proxies require 3–4 retry attempts per successful request. At high volume, that retry overhead in both time and cost often exceeds the price difference between the two types.
-
Mobile Proxies
Mobile proxies use IP addresses assigned by cellular carriers on 4G, LTE, and 5G networks. Carrier IPs are among the most trusted sources on the internet because they're shared by thousands of legitimate users. Blocking a single mobile IP risks cutting off real customers, so targets are reluctant to ban them aggressively.
Mobile proxies carry a block rate of 8–15%, lower than datacenter but higher than residential (IPRoyal Market Report, 2025). They're strongest for app-level access, mobile-specific geo-targeting, and checks that distinguish mobile from desktop traffic behavior. Cost is the highest in this category: $15–$25+ per GB.
-
ISP (Static Residential) Proxies
ISP proxies combine the speed of a datacenter with the legitimacy of a residential address. The IP is registered with an actual ISP but hosted on datacenter hardware. You get response times of 10–30 ms alongside block rates of 5–10%: the best speed-to-legitimacy ratio available.
They're the preferred choice for account management, long-duration monitoring, and any task where you need a persistent, consistent IP that won't get flagged mid-session. According to ProxyEmpire, ISP proxy adoption grew 43% year-over-year in 2024 among enterprise data collection teams, driven by session continuity advantages over rotating residential pools (ProxyEmpire State of Proxy Market, 2025).
-
-
Forward Proxy vs Reverse Proxy: What Is the Difference?
Proxy architecture splits into two fundamentally different orientations. Confusing them is one of the most common mistakes in networking discussions and job postings. A forward proxy acts on behalf of clients; a reverse proxy acts on behalf of servers.
A forward proxy sits between users and the internet. Your browser sends requests to the forward proxy, which forwards them to external sites. This is the configuration used for web scraping, privacy browsing, geo-unblocking, and content filtering. The receiving server sees only the proxy's IP.
A reverse proxy sits in front of a web server. External users send requests to the reverse proxy, which routes them to backend servers. This is the architecture behind every major web application: NGINX, Cloudflare, and AWS ALB all function as reverse proxies. Users see only the proxy's address; backend servers stay hidden.
Over 50% of the top 1 million websites use a reverse proxy layer for load balancing, SSL termination, or DDoS mitigation (W3Techs Web Technology Survey, 2025). You're hitting a reverse proxy almost every time you load a major website.
Our finding: Forward proxies are a client-side concern; reverse proxies are a server-side concern. They solve different problems in different directions. The clearest test: "Am I protecting clients from the internet, or protecting servers from clients?" Forward proxy for the first, reverse proxy for the second.
Here's a quick-reference comparison:
| Dimension | Forward Proxy | Reverse Proxy |
|-----------|--------------|---------------|
| Acts on behalf of | Clients / users | Servers / backends |
| Hides | Client IP from server | Server IPs from clients |
| Common tools | Squid, Privoxy, commercial proxies | NGINX, HAProxy, Cloudflare |
| Primary use | Privacy, filtering, scraping | Load balancing, SSL, caching |
| Who controls it | Client-side admin or user | Server-side operator |
-
What Proxy Protocols Should You Know?
Not all proxies speak the same language. Protocol determines what types of traffic your proxy can handle, how authentication works, and whether the proxy can inspect or modify requests. Choosing the wrong protocol causes silent connection failures that are frustrating to debug.
HTTP/HTTPS proxies are the most common. HTTP proxies understand application-layer content and can filter, log, or modify requests and responses. HTTPS proxies (also called CONNECT proxies) tunnel encrypted traffic: the proxy sees the destination hostname but can't read the payload. Together, these two variants cover the vast majority of web traffic.
SOCKS4 and SOCKS5 operate at the transport layer. SOCKS proxies are protocol-agnostic: they'll tunnel HTTP, FTP, SMTP, or any TCP/UDP traffic transparently. SOCKS5 adds username/password authentication and UDP support, making it the preferred choice for general-purpose tunneling, database connections, and anything that isn't pure HTTPS.
According to NetScout's 2025 Threat Intelligence Report, HTTPS proxy traffic accounts for 87% of all proxy connections in enterprise environments, with SOCKS5 making up most of the remainder. The protocol mismatch is a real-world failure point: if your scraping tool expects an HTTP proxy but your provider delivers a SOCKS5 endpoint, the connection fails without a clear error.
Enterprise proxy traffic by protocol in 2025. HTTPS dominates due to encrypted web traffic volume; SOCKS5 handles non-HTTP use cases. Source: NetScout Threat Intelligence Report, 2025. SOCKS5 vs HTTP proxy comparison
-
When Should You Use a Proxy Server?
Proxies solve a specific class of problems. They're a targeted tool, not a universal network layer. Here are six scenarios where a proxy delivers clear, measurable value.
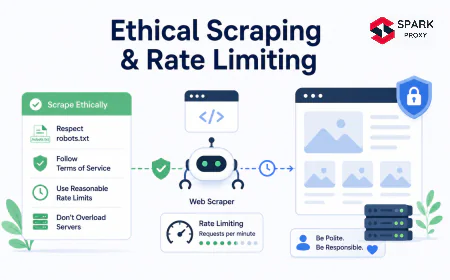
Web scraping at scale. Without a proxy, a scraper's single IP triggers rate limits after a few hundred requests. With a rotating pool, each request arrives from a different address, distributing load and avoiding block patterns. This is the dominant commercial use case for proxy services.
Geo-targeted data collection. Prices, search rankings, product availability, and ad placements differ by region. A proxy in Munich shows what a German user sees; a proxy in São Paulo reveals Brazilian pricing. No other tool delivers this level of localization for data collection purposes.
Corporate content filtering. Enterprise forward proxies block malicious sites, enforce acceptable use policies, and log traffic for compliance. According to Gartner, 78% of Fortune 500 companies operate some form of forward proxy for outbound web filtering (Gartner Enterprise Networking Survey, 2025).
Ad verification. Advertisers use proxies to confirm ads display correctly in target markets, detect fraudulent affiliate placements, and check whether competitors are copying creative assets. Mobile proxies are common here due to carrier IP trust levels.
Security research and penetration testing. Security teams use intercepting proxies to inspect, modify, and replay HTTP traffic between a client and a target application. Burp Suite, OWASP ZAP, and mitmproxy all function as local forward proxies for this purpose.
Bandwidth caching. A caching proxy on a corporate network stores frequently accessed content locally, reducing outbound bandwidth by 35–60% on well-configured deployments (Cloudflare, 2024).
From what we've seen: The most overlooked proxy use case is ad verification. Running international ad campaigns without proxy-based spot checks means flying blind on placement quality and affiliate compliance. It's a straightforward return on investment.
Enterprise proxy use case adoption rates. Content filtering and web scraping dominate; ad verification is growing fastest.
-
Proxy vs VPN: Which One Do You Need?
This is the most common point of confusion for anyone new to network privacy tools. Both proxies and VPNs route traffic through an intermediary server. The difference is scope, encryption, and purpose.
A VPN (Virtual Private Network) encrypts all traffic from your device at the OS level. Every application — your browser, email client, and background system updates — routes through the encrypted tunnel. VPNs are the correct tool for personal privacy, protecting traffic on public Wi-Fi, and accessing geo-restricted streaming services.
A proxy typically operates at the application level: usually your browser or a specific SDK. It doesn't encrypt traffic by default, and it only affects the app where it's configured. Proxies are the correct tool for structured, programmatic tasks: scraping, filtering, load testing, or any scenario where you need granular IP control across many concurrent connections.
Speed is a practical differentiator. Proxies introduce 1–10 ms of overhead. A well-optimized commercial VPN adds 5–20 ms; consumer VPNs can add 50–200 ms depending on protocol and server distance. At high scraping volume, that latency compounds significantly across thousands of requests per minute.
According to GlobalWebIndex, 31% of internet users accessed the internet via a VPN at least once a month in 2025 — but most proxy consumption happens programmatically through SDKs and scraping tools, not manual browser configuration (GlobalWebIndex Connectivity Report, 2025). The two tools serve genuinely different audiences.
The simplest rule: use a VPN for personal privacy; use a proxy for programmatic web access.
| Dimension | Proxy | VPN |
|-----------|-------|-----|
| Scope | Application-level | OS-level (all traffic) |
| Encryption | None by default (HTTP) | Always encrypted |
| Speed overhead | 1–10 ms | 5–200 ms |
| Best for | Scraping, geo-data, filtering | Personal privacy, Wi-Fi security |
| Cost | $1–$25/GB (type-dependent) | $3–$15/month flat |
| Concurrent IPs | Thousands (with rotation) | Single server IP |

Ready to get started? If you're building a data pipeline or scraper, begin with a datacenter proxy trial on a lightly protected target. Once you've validated your architecture, move to residential proxies for sites that enforce active bot detection. Most commercial providers offer free trials with 1–3 GB of bandwidth, which is enough to confirm whether the proxy type fits your target.
-
Conclusion
Proxy servers are a foundational networking tool that predates most of the modern web and underpins everything from corporate security infrastructure to billion-dollar data intelligence operations. The type you choose (datacenter, residential, mobile, ISP), the protocol (HTTP, SOCKS5), and the architectural orientation (forward vs reverse) each affect your block rate, cost, and performance in measurable, predictable ways.
The core points to retain: residential proxies offer the most legitimacy but cost more per GB; datacenter proxies are fast and cheap but blocked on protected targets; SOCKS5 handles more protocol types than HTTP; and forward proxies serve clients while reverse proxies serve servers.
Start with your use case, match it to the proxy type, and validate at a small scale before committing to volume. The infrastructure decisions you make at the start of a scraping or monitoring project are significantly harder to change once you're in production.
Frequently Asked Questions
A firewall filters traffic based on security rules — blocking unauthorized IPs, restricting ports, and preventing intrusions. A proxy server is an application-layer intermediary that routes, caches, and optionally filters traffic on behalf of a client or server. The two frequently run together: 68% of enterprise networks use a combined proxy-firewall architecture, according to Palo Alto Networks (2025 State of Network Security Report).
Free proxies carry significant security risks. Because the operator controls all traffic passing through the server, a malicious proxy can log credentials, inject ads, or strip HTTPS protections. A 2024 analysis by ProxyCheck.io found that 26% of free public proxies actively logged user traffic or injected content. For any sensitive task, use a paid provider with a clear privacy policy.
Yes. Anti-bot systems use several detection methods: checking whether the IP belongs to a known datacenter ASN, comparing IP geolocation against browser timezone and language settings, analyzing request headers for proxy signals such as X-Forwarded-For or Via, and behavioral analysis of request timing patterns. Residential proxies bypass most ASN-based checks; consistent request intervals and missing browser fingerprints can still reveal automation.
[INTERNAL-LINK: proxy detection avoidance → technical guide to bypassing anti-bot checks with header rotation and request randomization]
A transparent proxy intercepts traffic without any client-side configuration. The user doesn't know a proxy is in the path — typically deployed by ISPs for caching, by organizations for content filtering, or by attackers for traffic interception. The X-Forwarded-For header often reveals its presence. Unlike anonymous or elite proxies, transparent proxies pass your real IP to the target server.
The number depends on target rate limits and required throughput. A practical rule: if a site allows 1 request per IP per 5 seconds and you need 1,000 requests per minute, you need at least 83 unique IPs rotating through that window. For large-scale operations, rotating residential pools with 10,000+ IPs are standard. Most commercial providers offer APIs to manage IP rotation automatically.
[INTERNAL-LINK: proxy pool sizing guide → calculating the number of proxies required for scraping at different throughput levels]